Google's security research team has published a framework for responsibly disclosing quantum computing vulnerabilities in cryptocurrency systems. The paper, released through Google Research, addresses a problem the crypto industry has been quietly dreading for years: what happens when quantum computers become powerful enough to break the cryptographic foundations that secure billions of dollars in digital assets?
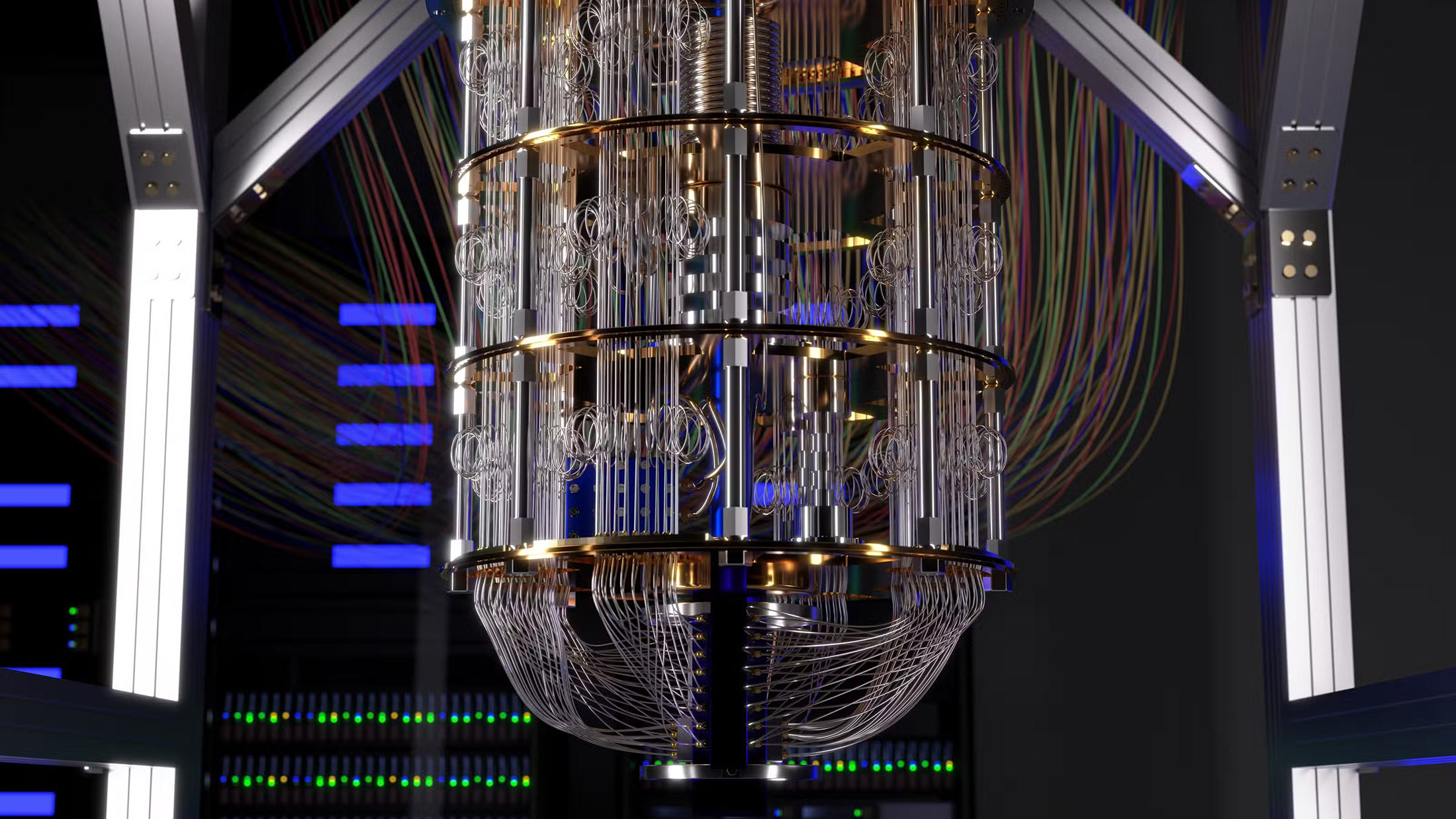
The timing matters. Quantum computing has moved from theoretical curiosity to engineering challenge, with companies like Google, IBM, and several well-funded startups racing toward fault-tolerant machines. The threat isn't immediate, but it's no longer abstract either. And the disclosure framework Google proposes isn't just academic. It introduces a novel application of zero-knowledge proofs that could reshape how the security community handles catastrophic vulnerabilities of any kind.
The Shor Problem
Most major cryptocurrencies rely on elliptic curve cryptography (ECC) to secure transactions and prove ownership of funds. Bitcoin, Ethereum, and dozens of others use variants of the same mathematical assumptions that have held up remarkably well against classical computers. But Shor's algorithm, developed in 1994, demonstrated that a sufficiently powerful quantum computer could solve these problems exponentially faster than any classical machine.
This isn't speculative cryptography. Shor's algorithm is proven mathematics. The only question is when quantum hardware will reach the scale necessary to execute it against real-world cryptographic keys. Estimates vary wildly, from five years to fifty, but the uncertainty itself is the problem. If a breakthrough happens faster than expected, billions in cryptocurrency could become vulnerable overnight.
The Google framework acknowledges this reality head-on. Rather than waiting for the crisis, it proposes a structured approach to identifying and reporting quantum vulnerabilities before they can be exploited.
Zero-Knowledge Disclosure
The most interesting element of Google's proposal isn't the vulnerability taxonomy or the coordination protocols. It's the use of zero-knowledge proofs as a disclosure mechanism.
Traditional responsible disclosure works on trust. A researcher finds a vulnerability, contacts the affected party, and hopes they respond appropriately before the researcher goes public. This model breaks down when the vulnerability affects decentralized systems with no central authority, or when the stakes are so high that even acknowledging the problem could trigger market panic.
Zero-knowledge proofs offer a different path. A researcher could prove they've discovered a genuine vulnerability without revealing the vulnerability itself. The proof demonstrates knowledge without disclosure. Affected parties can verify the claim is legitimate and begin remediation before any exploitable details become public.
This approach solves several problems simultaneously. It protects the researcher from accusations of fraud or extortion. It gives project maintainers confidence they're not chasing false alarms. And it buys time for fixes without creating information asymmetries that sophisticated attackers could exploit.
The Quantum-Resistant Exception
Not every cryptocurrency faces the same exposure. Zcash, launched in 2016, was designed from the ground up with both full transaction privacy and quantum resistance as core objectives. The protocol uses cryptographic techniques that don't depend on the same assumptions Shor's algorithm threatens.
This wasn't an afterthought. The Zcash team understood that privacy and security are inseparable over long time horizons. A transaction that's secure today but decryptable in twenty years offers only the illusion of privacy. Building quantum resistance into the foundation meant accepting performance tradeoffs and implementation complexity that other projects avoided.
The contrast is instructive. Most cryptocurrency projects optimized for speed, simplicity, or developer familiarity. They chose battle-tested cryptography that was well-understood and widely implemented. That made sense given the threats of 2015. It may prove shortsighted given the threats of 2035.
The Broader Lesson
Google's framework extends beyond cryptocurrency. The same zero-knowledge disclosure model could apply to vulnerabilities in chip manufacturing, critical infrastructure, or any system where the gap between discovery and exploitation could be catastrophic.
The underlying insight is that responsible disclosure requires more than good intentions. It requires mechanisms that align incentives, verify claims, and coordinate responses across adversarial boundaries. Zero-knowledge proofs provide mathematical guarantees that traditional communication cannot.
For the cryptocurrency industry specifically, the paper reads as a polite warning. Quantum computing timelines remain uncertain, but the window for orderly migration to quantum-resistant cryptography is not infinite. Projects that wait for proof of imminent threat may find the proof comes too late.
The transition won't be simple. Upgrading cryptographic foundations in live, decentralized systems involves coordination problems that centralized software doesn't face. But the alternative is hoping quantum computers stay conveniently slow forever. Based on Google's latest report, this is unlikely to be a successful strategy.