Security
Cybersecurity, surveillance, privacy, and the threats facing the digital world.
Advertisement

Policy
Texas Sues Discord to Enforce Age Verification. The Privacy Tradeoff Is About to Get Much Worse.
Texas Attorney General Ken Paxton filed suit against Discord last week, demanding mandatory age verification for all users. It's part of a global shift that trades one problem for another.

AI
Palantir Teases a New Vision for Apollo: AI Conquered Software Creation, Now Distribution Is the Battleground
Palantir's cryptic social media post signals a strategic reframing of Apollo as the infrastructure layer for AI-generated code deployment.

Security
Alleged OnlyFans Breach of 340 Million Records Circulates Online. The Claim Remains Unverified.
Social media posts allege a massive OnlyFans data breach exposing creator and user records. No evidence confirms the claim, but the risks it describes are real.
Security
Socket Flags 'TrapDoor' Campaign Stealing Crypto Wallets and Cloud Credentials Across npm, PyPI, and Crates.io
The supply chain security firm says it detected malicious packages within minutes of publication, as attackers target developers working on cryptocurrency, DeFi, and AI projects.

Tech
Manga Artist Loses Entire Google Account After AI Flags His Own Artwork on Drive
Japanese adult manga creator Masahiro Itosugi had his Google account permanently banned when he uploaded old manuscripts to Drive, reigniting debate over cloud moderation and the risks of centralizing your digital life.
Security
German Researchers Turn Standard WiFi Routers Into Near-Perfect Human Identification Systems
A team at Karlsruhe Institute of Technology demonstrated a system that identifies individuals with nearly 100% accuracy using only ordinary WiFi signals and machine learning.
Security
Anthropic's Glasswing Has Found Over 10,000 Critical Vulnerabilities. The Hard Part Is Fixing Them.
Project Glasswing has identified more than 10,000 high or critical-severity vulnerabilities in one month. The bugs were always there. The question now is whether defenders can patch them faster than attackers can exploit them.

Policy
Tulsi Gabbard Resigns as Director of National Intelligence, Citing Husband's Cancer Battle
The fourth Cabinet departure of Trump's second term comes as Gabbard's husband faces a rare bone cancer diagnosis. Principal Deputy Aaron Lukas will take over in an acting capacity.

Security
Your Smart Inverter Might Be Talking to Beijing. You'd Never Know.
Cheap consumer electronics from Amazon-style retailers are phoning home to servers in China, and new discoveries suggest the problem runs deeper than security researchers thought.

Security
Block's Spiral Launches Loupe, an AI Vulnerability Scanner for Open-Source Bitcoin Projects
Spiral, the Bitcoin-focused subsidiary of Jack Dorsey's Block, has released Loupe, a free AI-powered security tool designed to help under-resourced open-source Bitcoin projects defend against increasingly sophisticated threats.
AI
Google Detects First AI-Generated Zero-Day Exploit in the Wild
The Google Threat Intelligence Group says it disrupted a criminal campaign planning to use an AI-developed two-factor authentication bypass in a mass exploitation event.
Tech
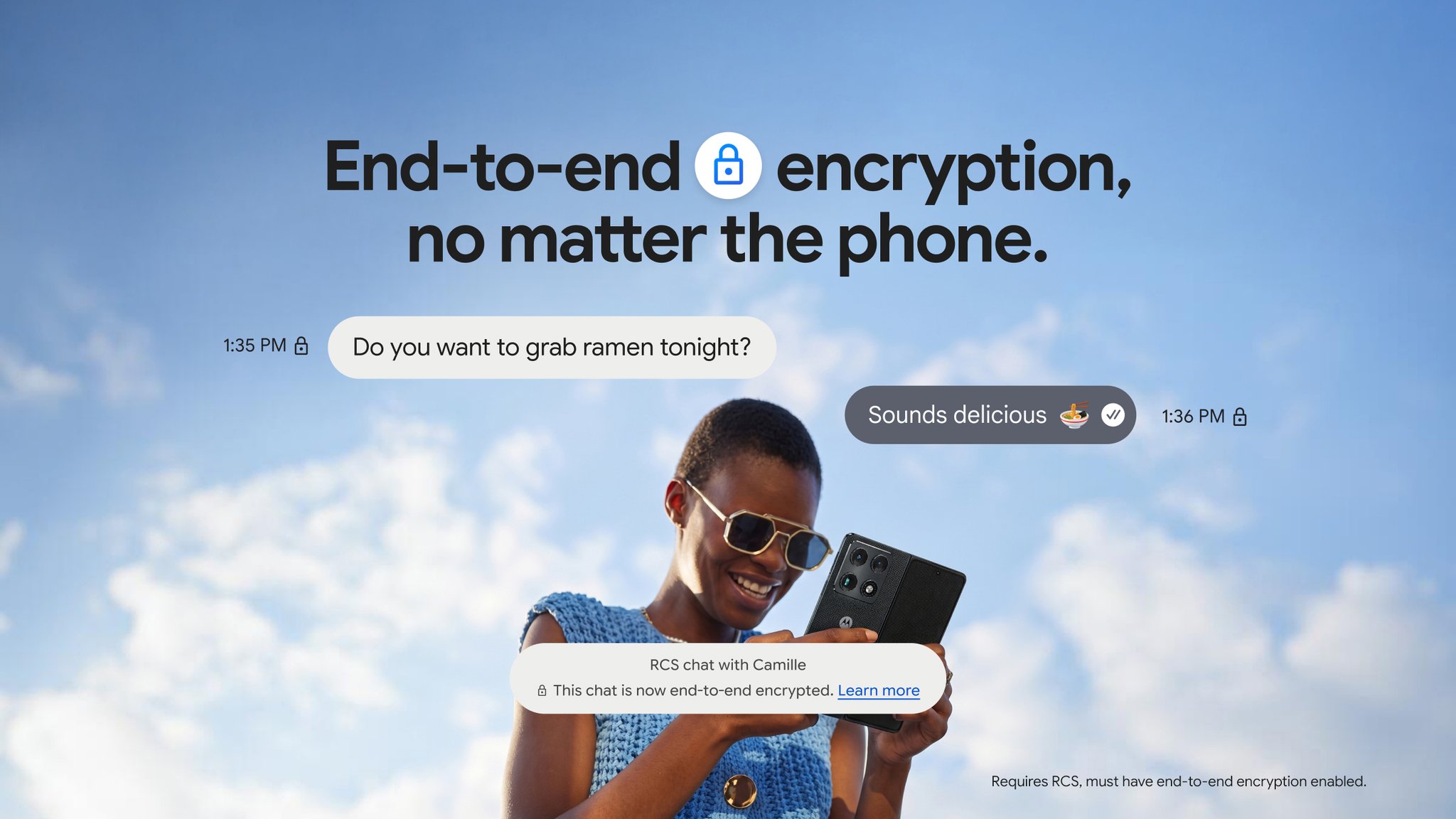
Google and Apple Ship Cross-Platform RCS Encryption, Closing the Last Major Privacy Gap in Mobile Messaging
iOS 26.5 and Google Messages now support end-to-end encrypted RCS conversations, making cross-platform text messaging secure for the first time without third-party apps.

Security
A Fake OpenAI Model Hit #1 on Hugging Face. It Was Malware.
A typosquatted repository impersonating OpenAI's Privacy Filter reached 244,000 downloads on Hugging Face before researchers caught the Rust-based infostealer hiding inside.

Policy
Utah's VPN Law Creates a Compliance Nightmare for Every Website Operator in America
Senate Bill 73 makes Utah the first state to hold websites legally responsible for users masking their location. Digital rights groups say it's technically unworkable.

Tech
Turkey's GATREX Previews a Future Where Drones Hunt Drones With Machine Gun Fire
Digitest's new counter-drone system mounts a six-barrel rotary machine gun on a heavy-lift UAV. It's an aggressive bet on kinetic defeat at SAHA 2026.
AI
OpenAI Rolls Out GPT-5.5-Cyber as the AI Arms Race for Digital Defense Enters a New Phase
OpenAI's cyber-focused model reaches vetted defenders weeks after Anthropic locked down Mythos, while insurers like Corgi race to underwrite the risks these tools are designed to find.
AI
Anthropic Just Read Claude's Hidden Thoughts For The First Time
The AI company is using a new technique to translate its models' internal numerical activations into plain English, catching deceptive behavior before it reaches users.
AI
X User Claims to Have Extracted GPT Image 2's Hidden Watermark. Here's What That Means.
OpenAI embeds invisible watermarks into AI-generated images, but a user on X says they've isolated the pattern. The implications cut both ways.
Security
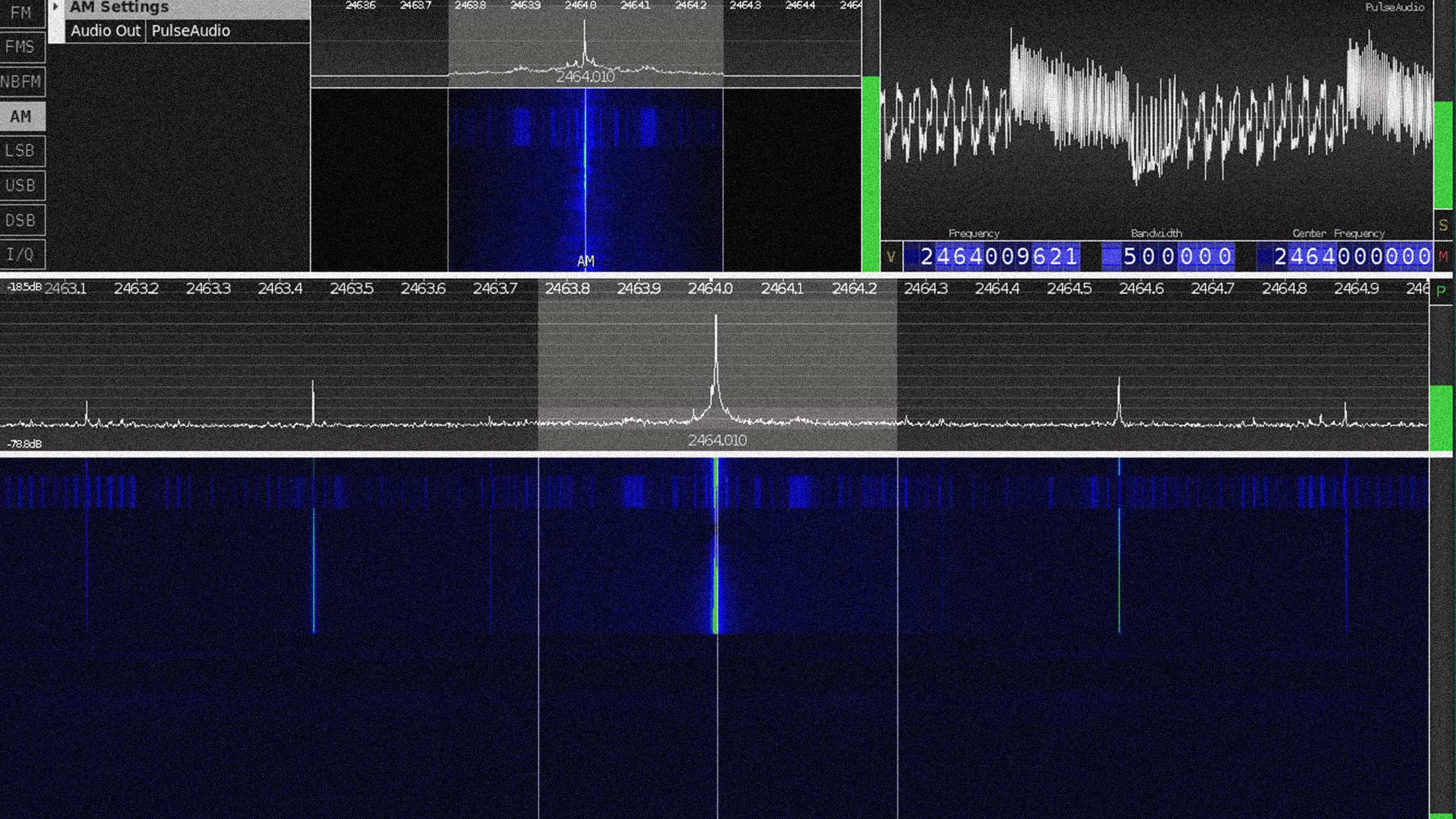
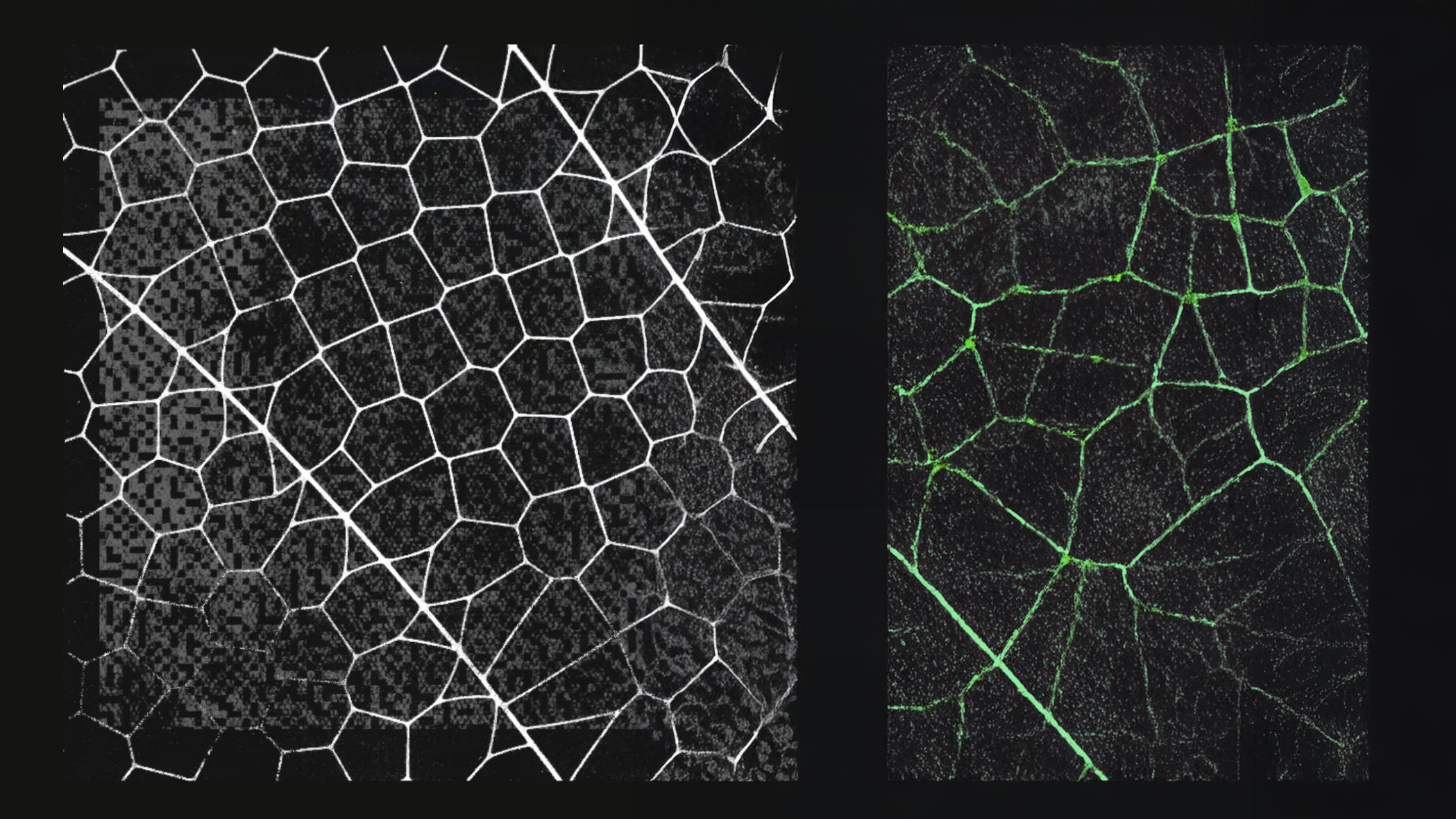
Screaming Channels: How Bluetooth Chips Broadcast Their Own Encryption Keys
Researchers at EURECOM recovered full AES-128 keys from a Bluetooth chip at 10 meters by listening to its radio emissions. The attack exploits a design flaw in mixed-signal chips.
Security
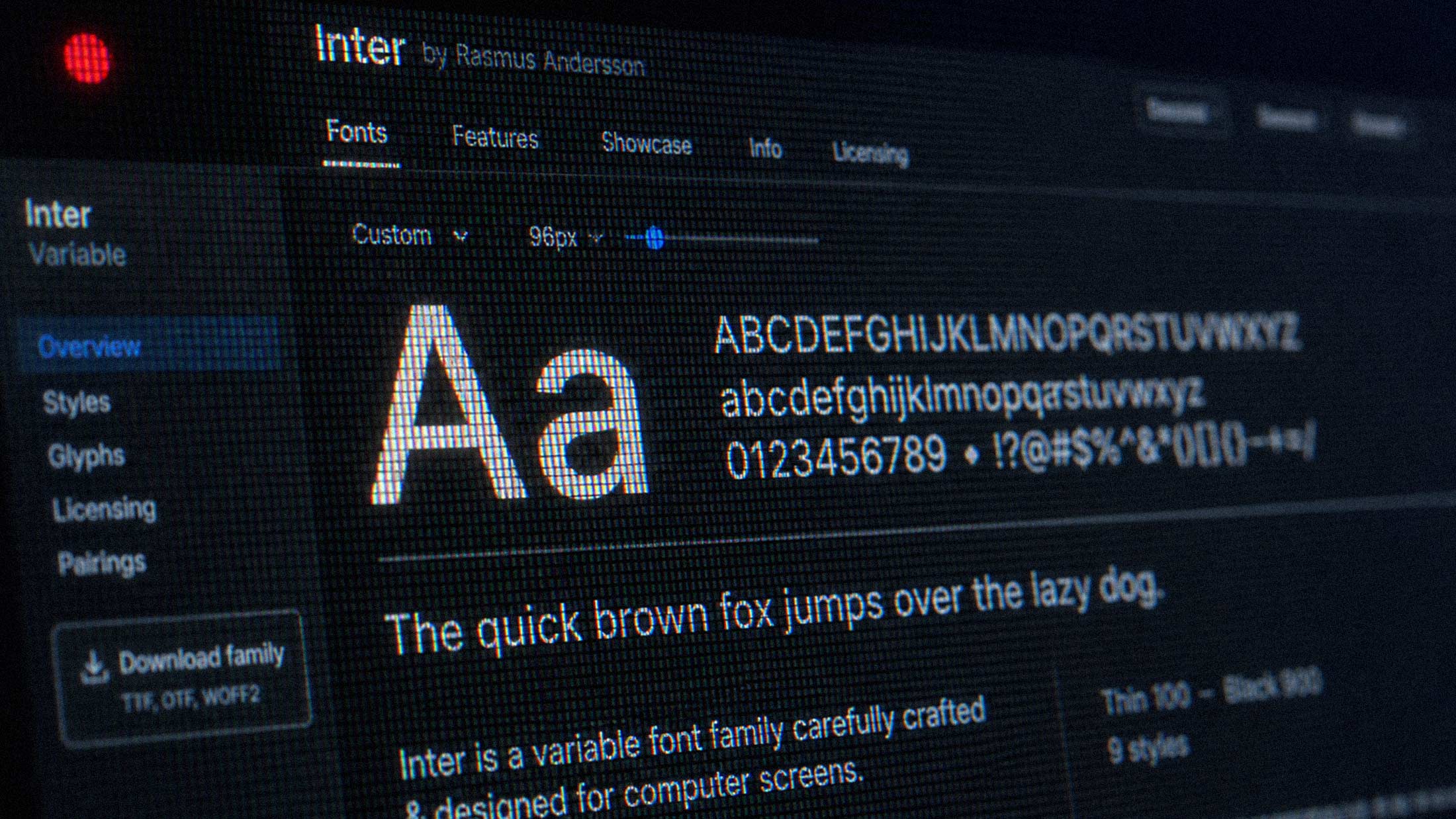
The Font on Your Website Is Reading You
Embedded web fonts from services like Google Fonts can function as silent tracking mechanisms, collecting IP addresses and feeding into broader fingerprinting systems that identify users across sites.

Tech
Hypercraft Razorback Arrives as a Mobile Power Grid for Autonomous Warfare
The Utah company's new unmanned ground vehicle carries 2,400 pounds of payload and exports 38 kilowatts, turning every forward position into an energy node.

Crypto
Is Zcash the Dark Horse the Crypto World Has Been Waiting For?
With government officials taking the stage at Bitcoin 2026 and quantum threats accelerating, the case for a privacy-focused, quantum-resistant alternative is stronger than ever.
AI
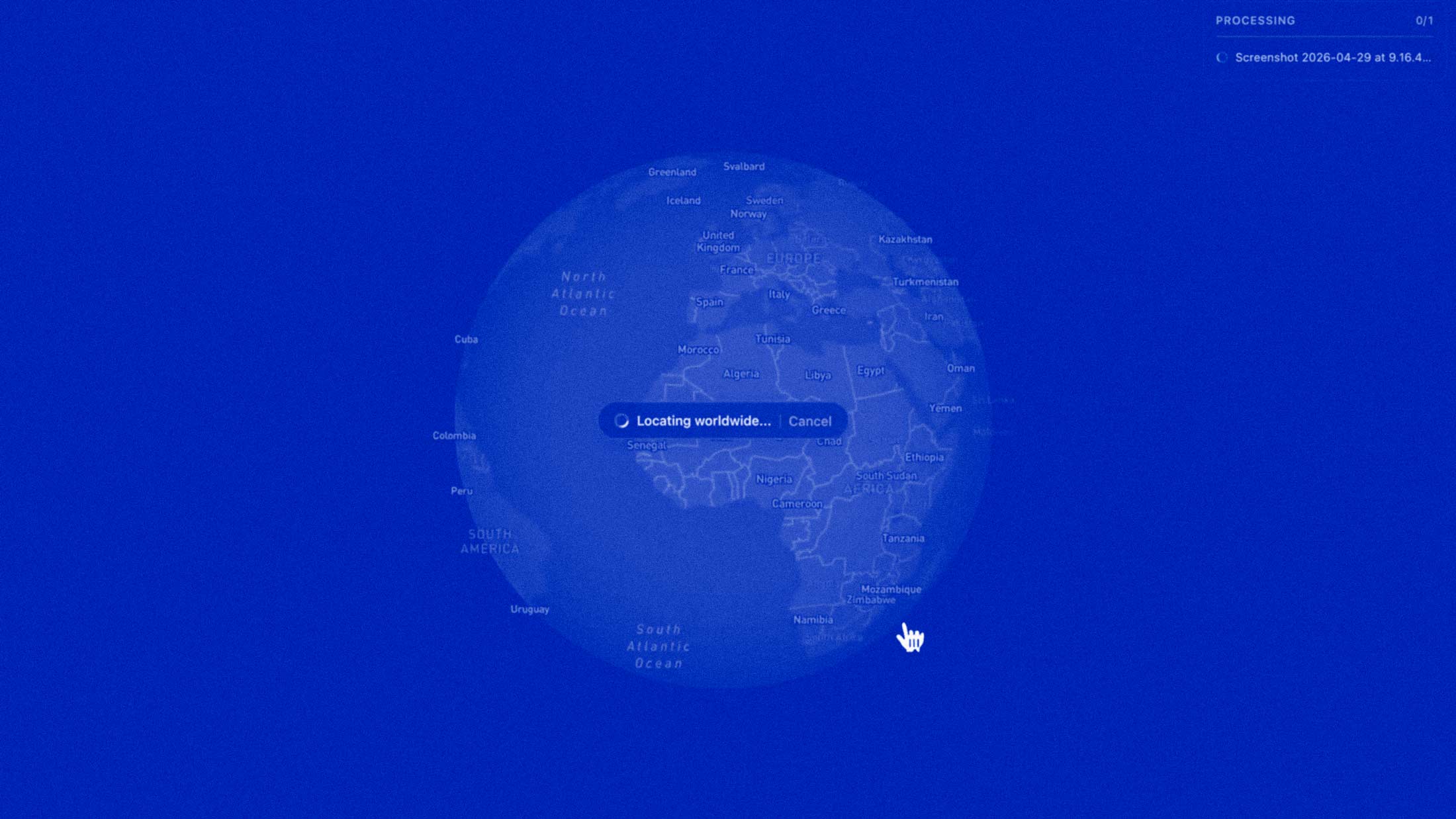
Graylark's Raven Turns Pixels Into Actionable Intelligence for Law Enforcement
The visual intelligence platform, formerly known as GeoSpy, reads vegetation, architecture, and soil to pinpoint locations in seconds without metadata or GPS.
Security
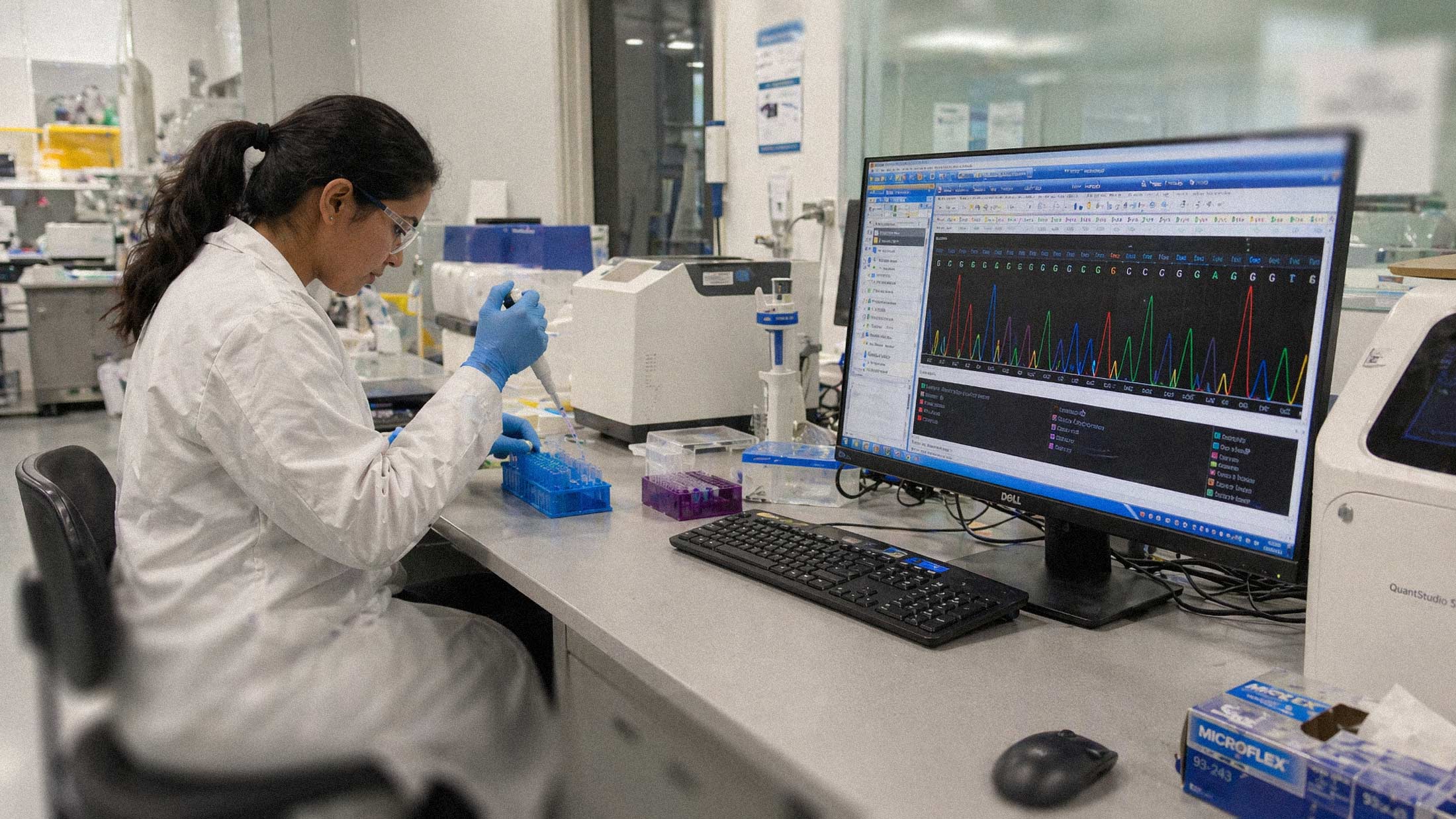
UK Biobank Data Found for Sale in China Exposes the Fragility of Centralized Health Databases
Half a million Britons' genetic and health records appeared on Alibaba. The breach underscores a growing vulnerability in centralized medical data systems.
Security
Lovable.dev Fixed a Critical Bug for New Projects and Left Every Old One Exposed
A five-API-call IDOR vulnerability gives any free Lovable account access to source code, database credentials, and live customer data from every project created before November 2025.

Tech
Teledyne's Black Hornet 4 Is the Pocket-Sized Drone Redefining Tactical Reconnaissance
At 70 grams, the Black Hornet 4 fits in a soldier's palm but delivers battlefield intelligence that used to require entire teams.
Advertisement

Security
Vercel Discloses Security Incident Involving Unauthorized Access to Internal Systems
The hosting platform confirmed a limited subset of customers was affected and has notified law enforcement. Details remain sparse.

Tech
Your Smart TV Is Screenshotting Everything You Watch, Every 15 Seconds
A peer-reviewed study confirms LG, Samsung, and other smart TVs silently capture and transmit what's on your screen, even from gaming consoles and laptops.
AI
Researchers Are Teaching AI to See Through Clothes and Walls Using Radar
A new system called mmAnomaly pairs radar with diffusion models to detect threats where cameras can't go, hitting 94% accuracy.

Security
Kraken Says It Won't Pay Extortionists Threatening to Leak Internal Videos
The crypto exchange disclosed two insider-access incidents affecting about 2,000 accounts and is working with federal law enforcement.

Tech
X Spins Off XChat as a Standalone Encrypted Messenger. Signal Should Pay Attention.
Elon Musk's X launches a dedicated encrypted chat app. It promises Signal-level privacy, but the fine print tells a different story.
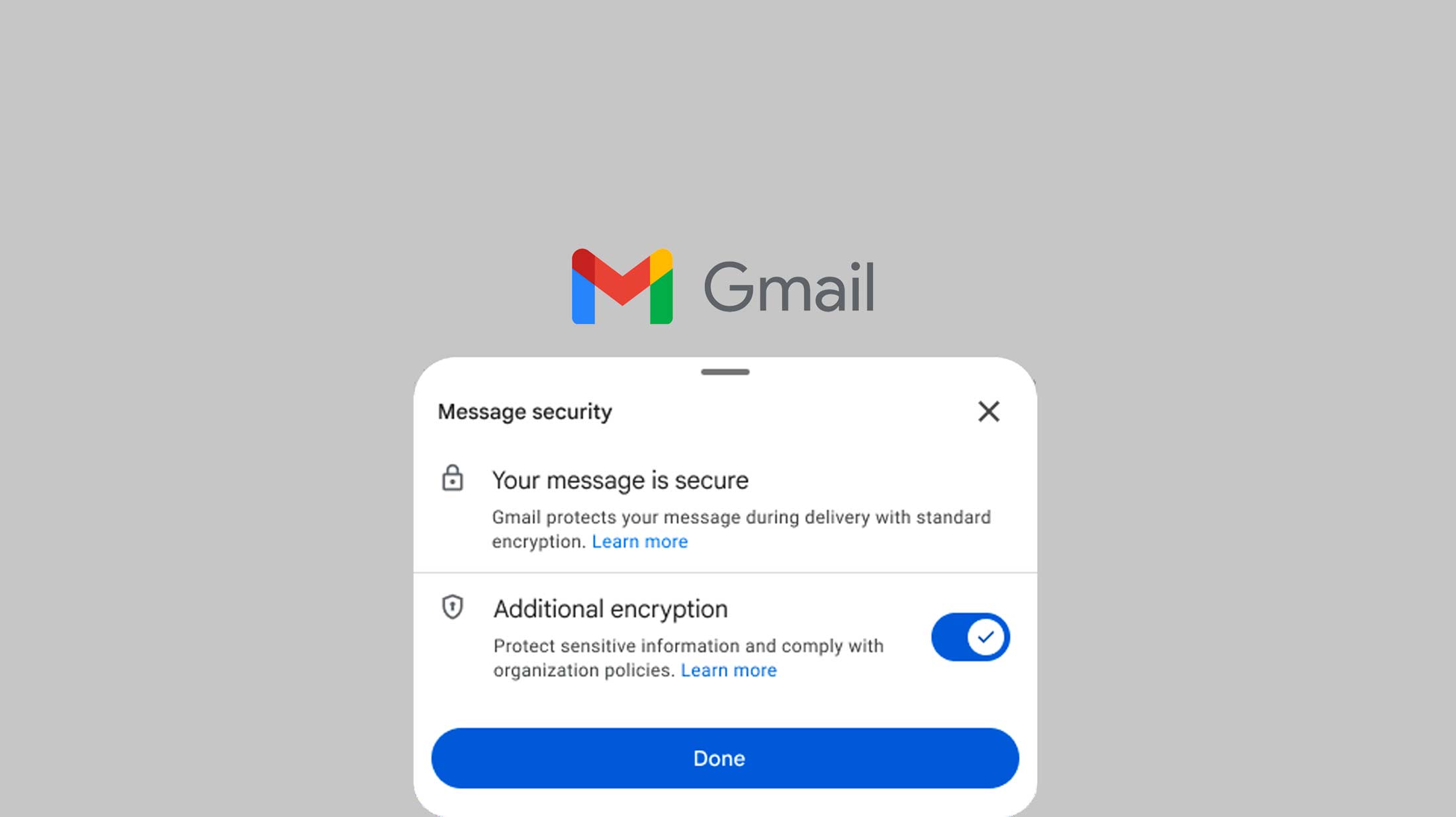
Security
Gmail Brings End-to-End Encryption to Mobile, But the Fine Print Matters
Google's native E2EE for Gmail on Android and iOS marks a significant shift for enterprise security, though consumer rollout remains unclear.
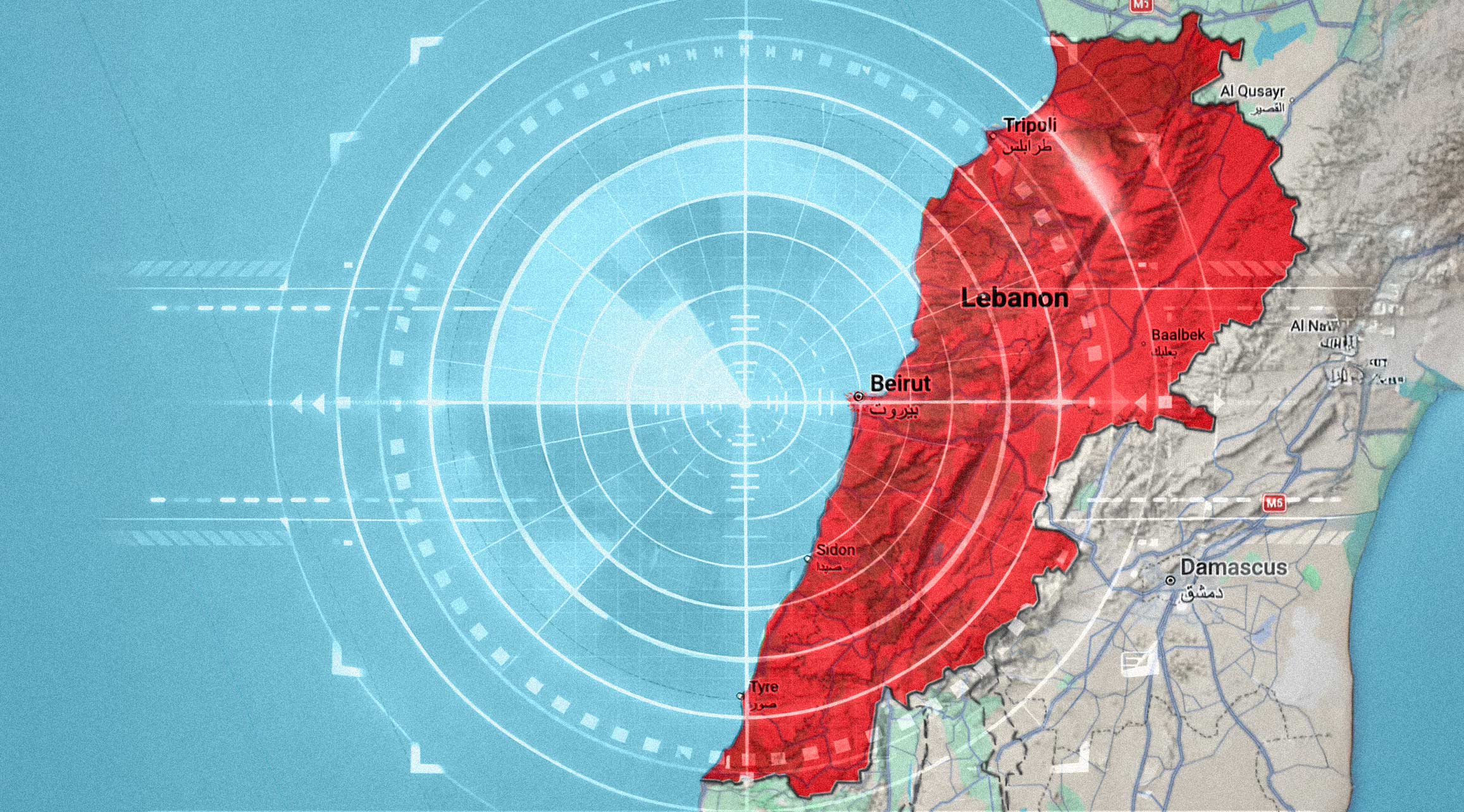
AI
Inside the IDF's AI Data Factory Driving Strikes Across Lebanon
Israel's military has built an industrial-scale intelligence machine that identifies targets faster than any human analyst could. The implications are profound.

Security
The FBI Found a Way to Read Signal Messages. It Didn't Require Breaking Encryption.
Deleted Signal messages were recovered from an iPhone's notification database, raising questions about where encrypted data actually lives.
AI
Anthropic Built the Best Bug Hunter in AI. Then Decided Not to Release It.
Mythos can find vulnerabilities faster than any model before it. That's exactly why Anthropic is keeping it locked down.
Tech
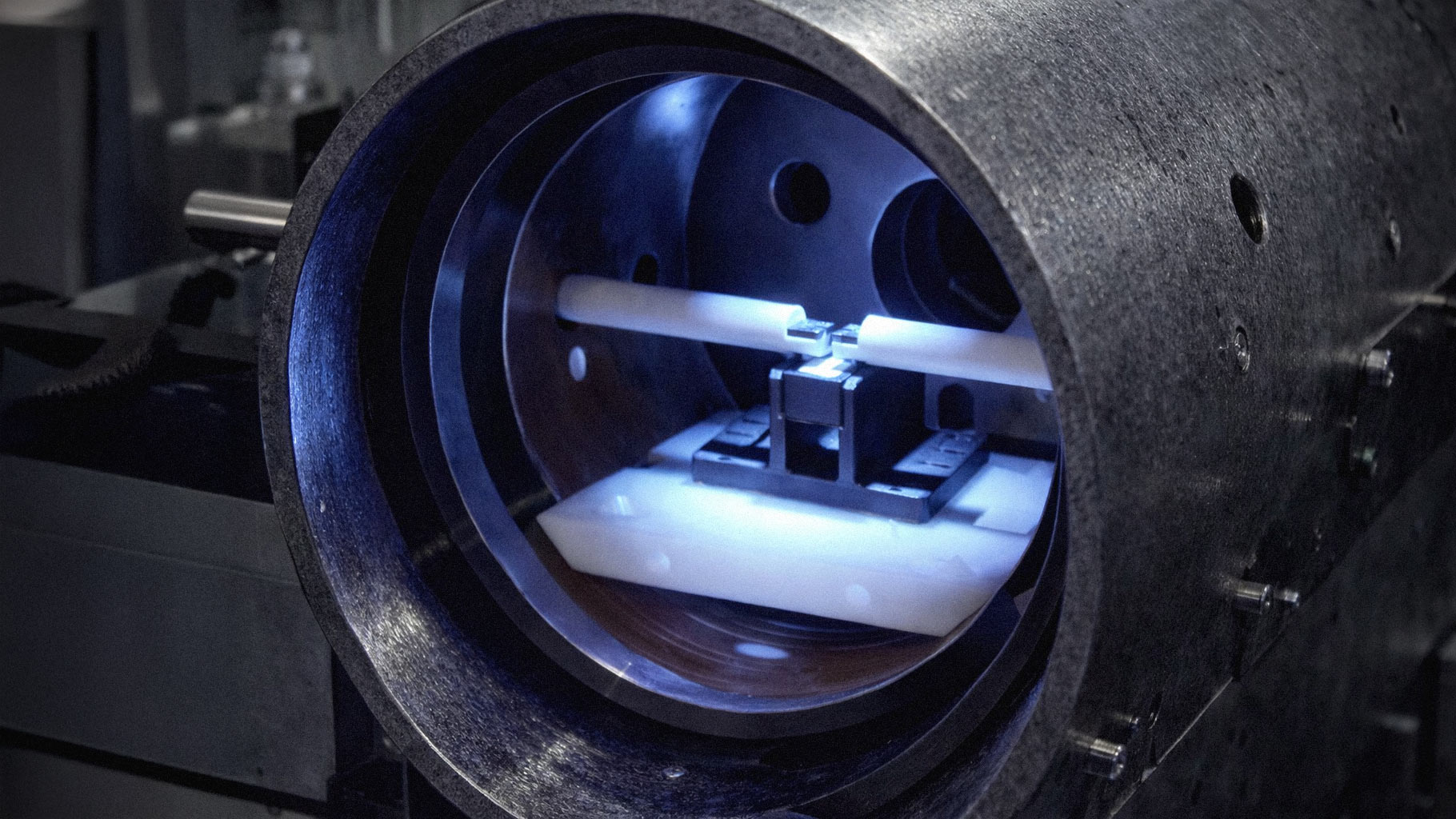
Ghost Murmur: The Quantum Technology That Found a Missing Pilot in Iran
The CIA's use of quantum magnetometry to locate a downed F-15 pilot marks a turning point in both military sensing and commercial tech.

Policy
China Removes Bitchat From App Store, Citing Social Mobilization Risk
The CAC ordered Bitchat's removal under provisions targeting apps capable of influencing public opinion—a familiar playbook for silencing encrypted communication.

Tech
What Tech Survives a Nuclear War?
A practical assessment of which devices work after electromagnetic pulse, nuclear winter, and the collapse of centralized infrastructure.

Security
US Forces Extract Downed F-15 Pilot From Iranian Territory as Search for Second Continues
A combat search and rescue operation deep inside Iran marks the first such mission since the failed 1980 hostage rescue attempt.

AI
Iran's Threat to UAE Stargate Project Exposes AI's Geopolitical Soft Underbelly
A viral Iranian video targeting Microsoft and OpenAI's $100B+ AI supercluster reveals how geopolitics has become the defining risk to the global AI boom.

Security
Iran's Cyber Offensive Against Big Tech Is No Longer a Background Threat
Trump's strikes and Tehran's response have pushed Iranian hacker activity into overdrive, with Silicon Valley now squarely in the crosshairs.
Science
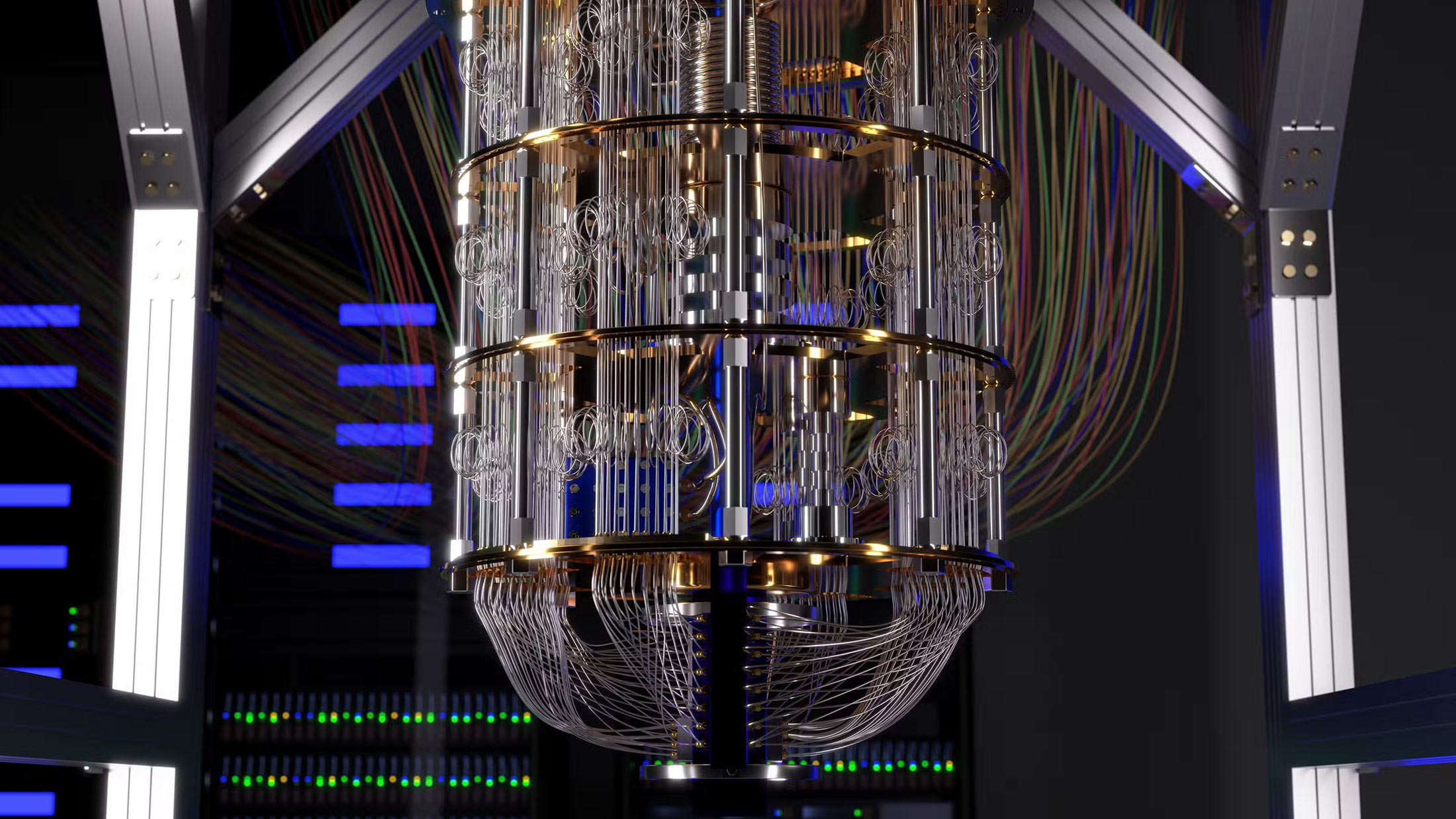
Quantum Computing's Scaling Problem Isn't About Size. It's About Noise.
The race to build useful quantum computers has hit a fundamental barrier: the machines get noisier as they get bigger.

Policy
Your Feed Is Now a Border Checkpoint
The U.S. now requires visa applicants to unlock their social media before interviews. The surveillance state just got a lot more personal.
Crypto
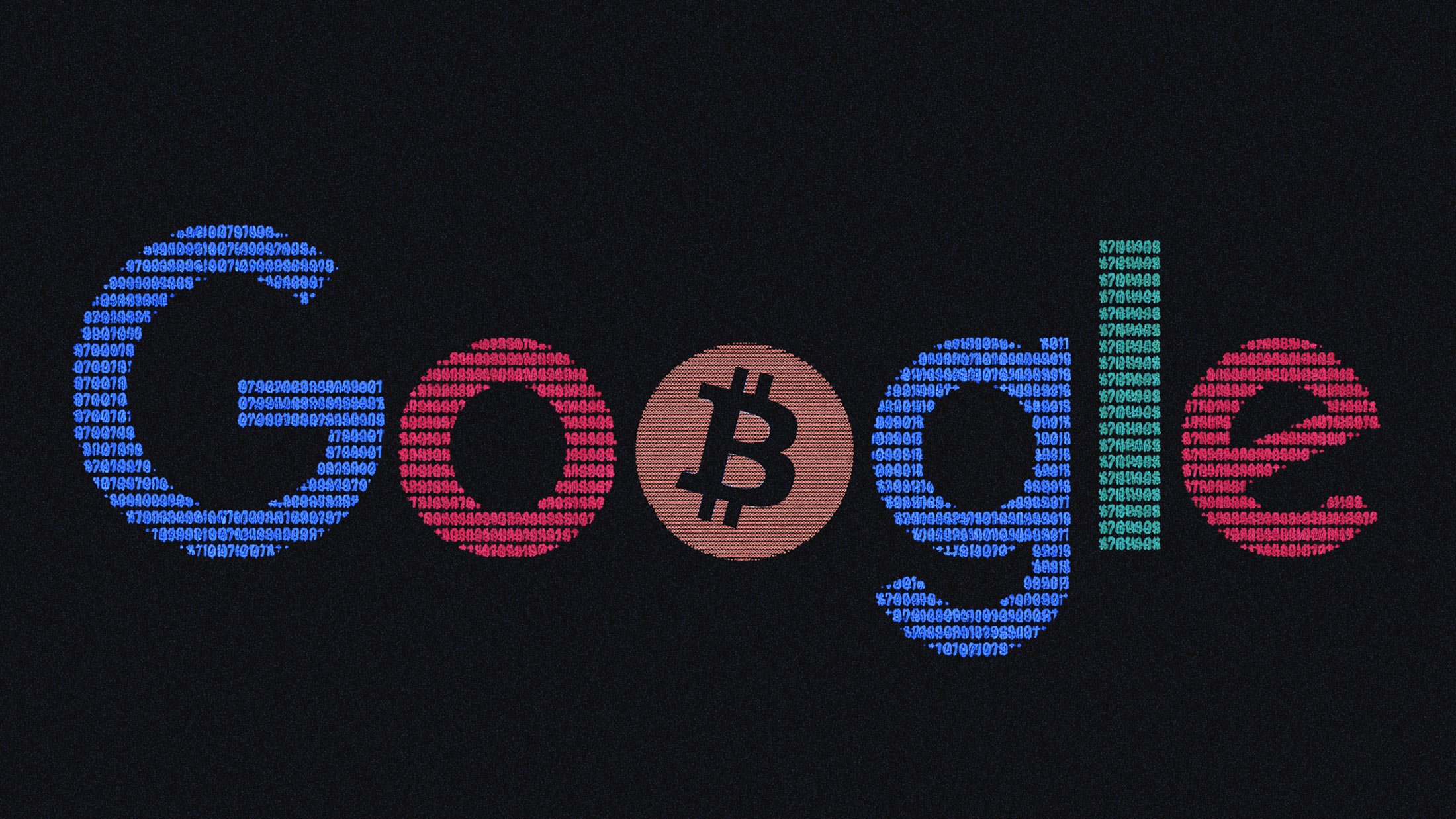
Google's Quantum Disclosure Framework Is a Warning Shot for Crypto
A new responsible disclosure model uses zero-knowledge proofs to report quantum vulnerabilities—before they become catastrophic.

Crypto
Zcash's Tachyon Upgrade Is a Bet That Privacy Still Matters
The upcoming protocol overhaul promises faster, cheaper shielded transactions—and a renewed argument for financial privacy in an age of surveillance.

Tech
The Tech Powering Iran's Shadow War Is Older Than You Think
From decades-old air defense systems to cutting-edge drones, Iran's military tech tells a story of sanctions, ingenuity, and borrowed time.

Tech
16 Billion Credentials Exposed: Inside the ‘Mother of All Data Breaches'
Over 16 billion login credentials exposed from misconfigured databases, affecting major platforms like Apple, Google, and Facebook. Learn protection tips and understand the breach's magnitude.

Crypto
Solana Cofounder’s KYC Leak Sparks Fresh Fears Around Coinbase Hack
A KYC photo leak tied to a Solana cofounder—disseminated via a hacked Instagram account—has added a disturbing new chapter to the ongoing Coinbase hack fallout.

Crypto
Cetus Exploit on Sui Hits Hard—and Exposes a Bigger Problem
Sui’s flagship DEX, Cetus, was hit by a flash loan exploit—draining liquidity and sending CETUS down 90%. It’s a harsh reminder that even the newest chains aren’t immune from the oldest DeFi risks.

Crypto
Crypto Gets Physical: The Rise of On-Chain Kidnapping
Crypto is borderless. Crime isn’t. France’s recent wave of violent kidnappings tied to crypto wealth is a wake-up call that anonymity and liquidity are double-edged swords. The solution isn’t retreat—it’s real-world resilience.

Crypto
Coinbase Exposes Insider Breach and Extortion Attempt, Offers $20M Reward Instead of Paying Ransom
Coinbase has revealed a data breach involving bribed support agents and a $20 million extortion attempt. The crypto exchange refused to pay, is reimbursing affected users, and is offering a $20M reward for information leading to the attackers’ arrest.

Crypto
5 Things to Know About Solana’s Zero-Day Bug Fix
Solana patched a critical zero-day vulnerability within 48 hours—here’s what happened, why it matters, and how it’s fueling new debates about decentralization and governance.
