Typography as Surveillance
When a designer picks a typeface for a website, privacy is rarely part of the conversation. But Google Fonts appears on roughly 54% of desktop sites and 47% of mobile sites, and every request to that service carries data that privacy regulators increasingly view as personal information.
The mechanics are simple. The Google Fonts API does not set cookies, but when embedding fonts via the Web API, Google receives the user's IP address, the requested URL, and HTTP headers including the user agent and referer. That means Google knows which site you visited, what browser and operating system you're running, and your approximate location. Google states it does not use this information to build profiles or for targeted advertising. Privacy advocates have reasons to remain skeptical.
A German Court Draws a Line
In January 2022, a Munich court changed the calculus for European website operators. The Landgericht München ordered a website to pay €100 in damages for transferring a user's IP address to Google via the Fonts library without consent. The amount was trivial. The precedent was not.
The court ruled that an IP address constitutes personal data because operators could combine it with other information to identify individuals. It deemed irrelevant whether Google actually linked the address to anyone. The mere transmission without consent was the violation. Future infringements would carry penalties of €250,000 or six months imprisonment.
Since that ruling, legal analysts have noted that the decision exposes millions of websites to potential GDPR non-compliance fines, given the ubiquity of the service. Website owners face a straightforward choice: obtain explicit consent before loading external fonts, or host them locally.
Beyond IP: The Fingerprinting Problem
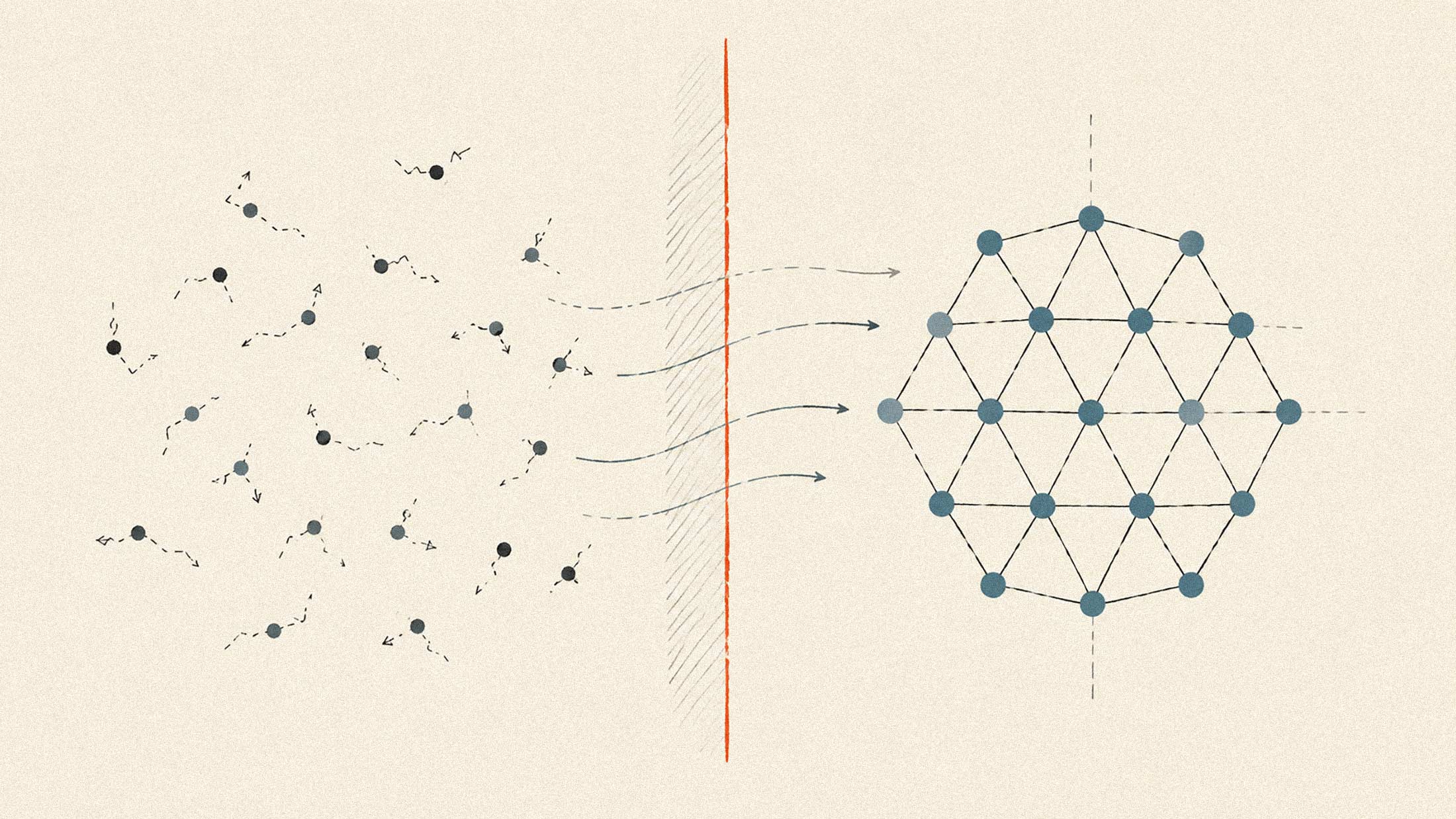
The IP address issue is only one layer of font-related tracking. A separate technique, font fingerprinting, exploits the fonts installed on your device to build a unique identifier that persists even when you clear cookies or use private browsing.
Font fingerprinting techniques measure the dimensions of text or individual Unicode glyphs and enumerate fonts to find rendering differences. This method creates a unique fingerprint that is difficult to spoof or alter. A script can quietly probe whether your system has Helvetica Neue, Adobe Caslon, or the unusual font that came bundled with some software you installed years ago.
Installed fonts are a surprisingly high-entropy signal. A script measures how wide a string renders in a known-missing font, then re-measures it in each candidate font. If the measurements differ, the font is installed. Run this check across a few hundred typefaces, and you have a detailed inventory. A designer with 50+ professional fonts is far more identifiable than someone with just system defaults. Font lists alone can make users unique among tens of thousands.
According to EFF research, over 84% of browsers are uniquely identifiable by fingerprint alone, and modern anti-fraud systems that track 100+ signals push that figure above 95%. Your font collection is one piece of a mosaic that also includes your screen resolution, GPU characteristics, audio processing quirks, and TLS handshake patterns.
The Consent Problem
The core problem with IP address processing via Google Fonts is that it is not strictly necessary. Sites can avoid the data transfer entirely by hosting fonts locally. But asking users for permission before loading a typeface presents absurd user experience challenges. In practice, controllers cannot feasibly request such permission. It would collapse traffic numbers or leave websites displaying fallback Arial.
This leaves self-hosting as the only realistic compliance path. About 31.5% of desktop sites and 36.4% of mobile sites now use exclusively self-hosted fonts, up from about 30% last year. The shift is accelerating. Services like Google Webfonts Helper and WordPress plugins like OMGF simplify the process of downloading font files and serving them from your own domain.
What Users Can Do
For individuals, the situation is harder to address. Clearing cookies, switching to a private window, or resetting your browser does not change your fingerprint, because your GPU, screen size, font list, and audio stack remain constant. VPNs hide your IP but do nothing about the other signals. Privacy-focused browsers like Tor and Brave offer some anti-fingerprinting protections, but they introduce friction and can break site functionality.
The uncomfortable reality is that fonts have become part of the web's surveillance infrastructure. What appears to be a design choice is also a data pipeline. Site operators who care about user privacy should consider the data flows their technology stack creates. And users should understand that typography, like nearly everything else on the modern web, comes with strings attached.