A Bluetooth chip can inadvertently broadcast the encryption keys it is supposed to protect. Researchers at EURECOM's System Security Group have demonstrated a class of side-channel attacks they call "Screaming Channels," which exploit electromagnetic leakage from mixed-signal chips to recover AES-128 keys at distances up to 15 meters in real-world environments.
The Physics of the Leak
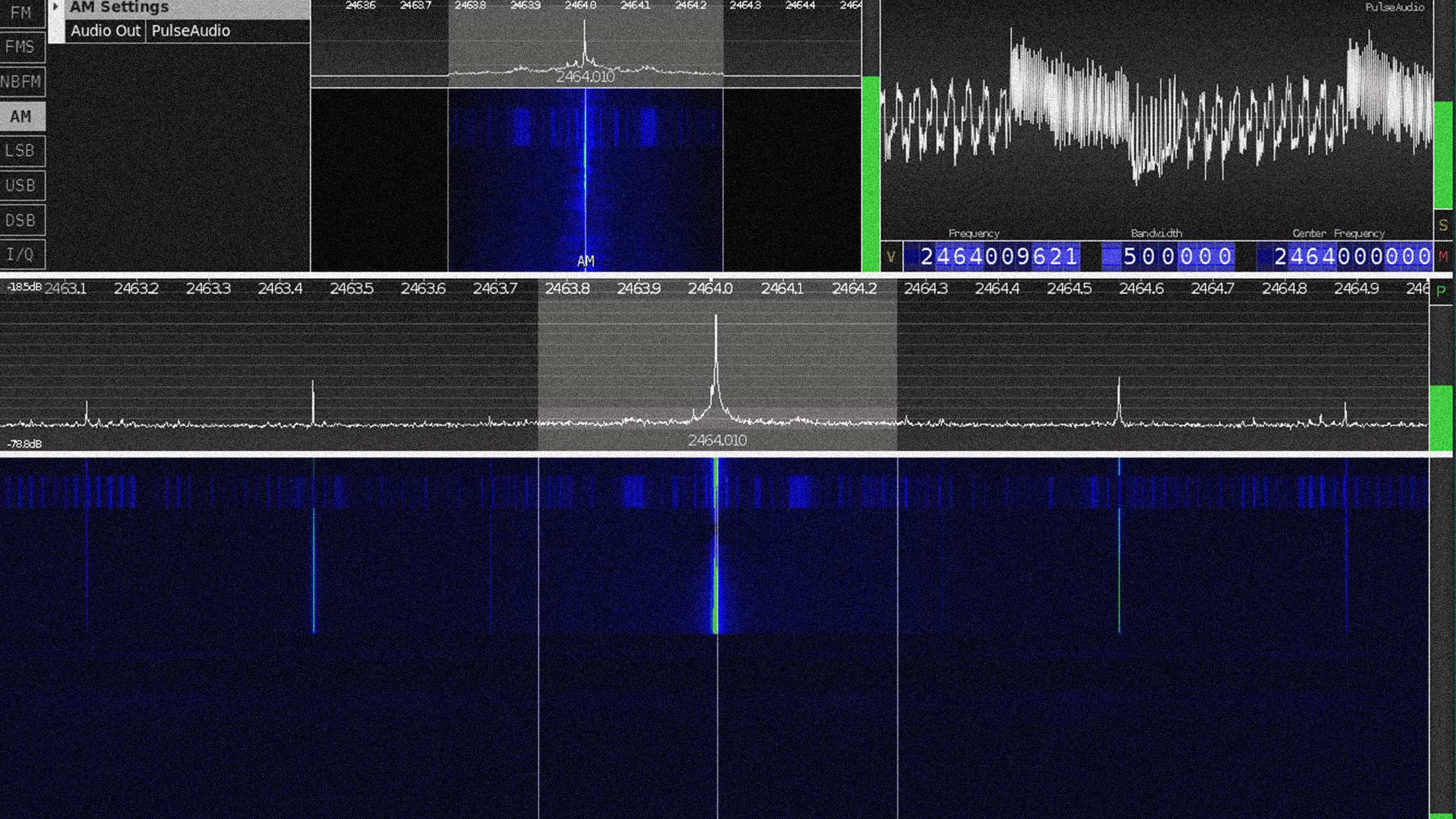
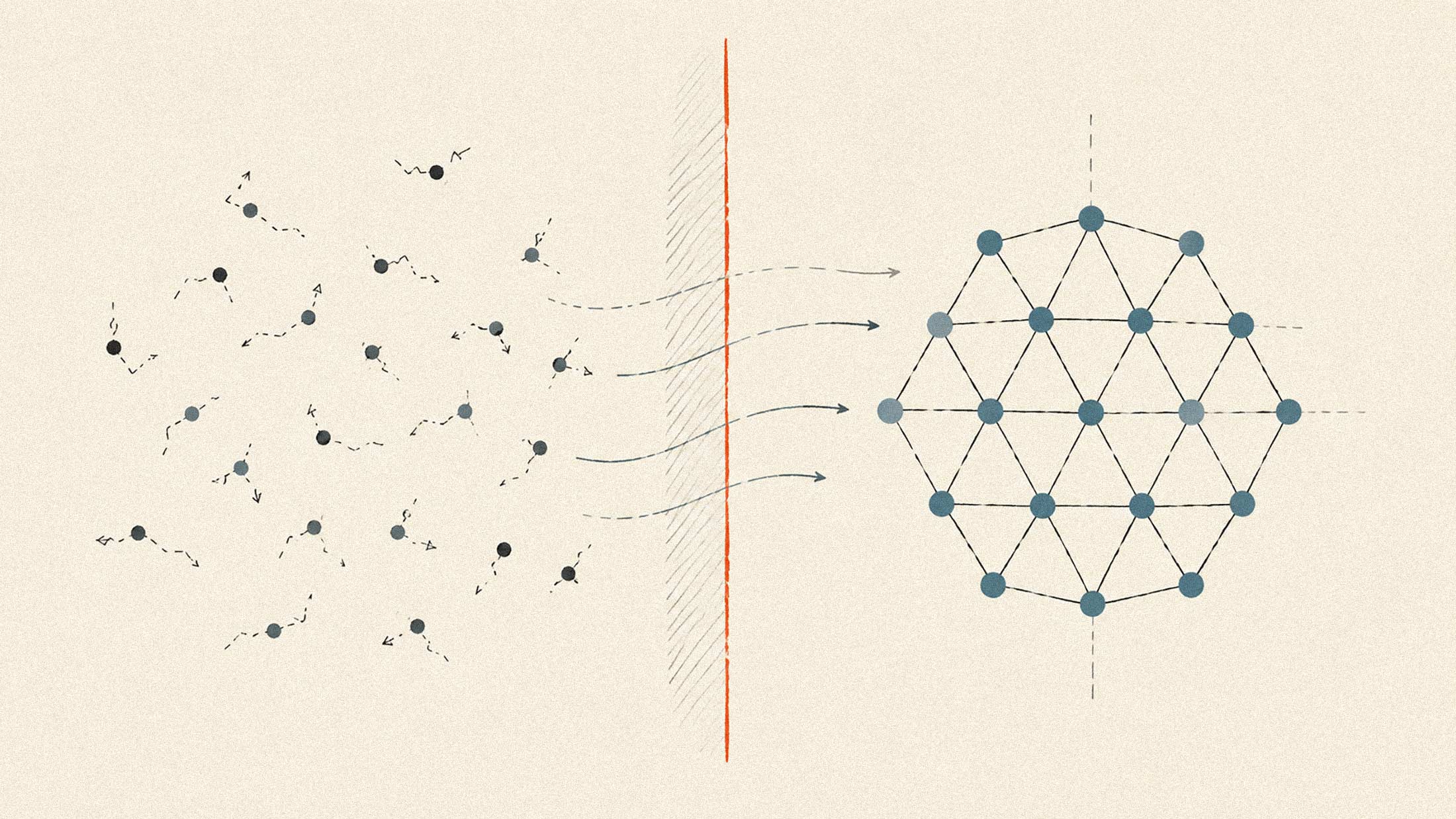
Traditional electromagnetic side-channel attacks require an attacker to get within centimeters of a target device, typically using specialized probes. Screaming Channels extends that range by orders of magnitude. The vulnerability arises because modern wireless chips combine digital processing and analog radio circuitry on the same silicon die. While the processor runs cryptographic operations, electrical noise from those computations couples into the radio transmitter chain. That noise gets modulated onto the 2.4 GHz carrier signal, amplified, and transmitted through the chip's own antenna.
The EURECOM team, led by Giovanni Camurati and Aurélien Francillon, targeted the Nordic Semiconductor nRF52832, a popular Bluetooth Low Energy chip built around an ARM Cortex-M4 core. During AES encryption, the ten rounds of the cipher are clearly visible in the time-domain radio signal. An attacker with a software-defined radio can capture these emissions, align the traces, and apply standard correlation or template attacks to extract the full key.
Demonstrated Attacks
The initial proof-of-concept recovered the complete AES-128 key from the tinyAES implementation at 10 meters using template attacks conducted in an anechoic chamber. A separate correlation attack retrieved the mbedTLS implementation's key from 1 meter. Follow-up research pushed practical key recovery to 15 meters in a standard office environment, using a device profiled months earlier via cable connection. The researchers also detected data-dependent leakage at 40 meters and extracted AES traces at 60 meters.
In 2024, the same research group published "BlueScream," which demonstrated the attack against stock Bluetooth Low Energy firmware rather than instrumented test code. By manipulating BLE protocol timing to maximize transmission duration during key derivation, the researchers achieved full key recovery with instrumented firmware and partial key recovery against unmodified production software.
Why This Matters for Crypto Wallets
The implications for Bluetooth-enabled hardware wallets are worth examining. Many popular cryptocurrency wallets use Bluetooth for mobile connectivity, and some are built on chips architecturally similar to the nRF52832. While modern secure-element-based wallets isolate private keys in tamper-resistant chips, the Screaming Channels research demonstrates that cryptographic operations happening outside the secure element remain vulnerable.
Side-channel attacks on hardware wallets are not theoretical. Researchers have extracted seed phrases using power analysis and voltage glitching. The difference with Screaming Channels is range. Traditional attacks require physical possession of the device or at minimum a few centimeters of proximity. Screaming Channels works from across a room, or through walls with spatial diversity techniques.
The researchers note that their attack is not specific to the Nordic chip. They observed similar leakage characteristics in Qualcomm Atheros Wi-Fi silicon and suggest that chips implementing other protocols including 4G/LTE and RFID should be inspected for the same vulnerability. The attack works against software AES implementations; hardware AES blocks on the same chips proved more difficult to attack, though the researchers reported partial success recovering four of sixteen key bytes.
Countermeasures
The EURECOM team recommends applying standard side-channel countermeasures such as masking and hiding to devices with mixed-signal architectures. Masking randomizes intermediate values during computation, while hiding aims to eliminate the relationship between computation and observable emissions. Neither is trivial to implement correctly, and both carry performance costs.
For users of Bluetooth-enabled security devices, the practical advice is straightforward: avoid using them in environments where an attacker could position receiving equipment within tens of meters for extended periods. Air-gapped designs using QR codes for data transfer eliminate the radio vector entirely.
The deeper question is whether mixed-signal chip design can evolve to prevent substrate coupling between digital and RF domains. Until then, any device that computes secrets while transmitting should be treated with suspicion. The chip is doing exactly what radio engineers designed it to do. The problem is that some of what it broadcasts was never supposed to leave the package.